A Quick Look at Some Enterprise VPNs Leaking Customer Data
Organizations subscribe to VPNs to protect their data from prying eyes, and yet some of these VPNs have vulnerabilities that allow attackers to gain access.
The hackers often turn off multi-factor authentication and view logs cached by the VPN servers as plain text to enable them to steal confidential information and plant ransomware.
Information from https://www.vpntesting.com/reviews/expressvpn reveals the different aspects of vulnerabilities that are commonly exploited during an attack.
Here are some of the latest VPNs attacks:
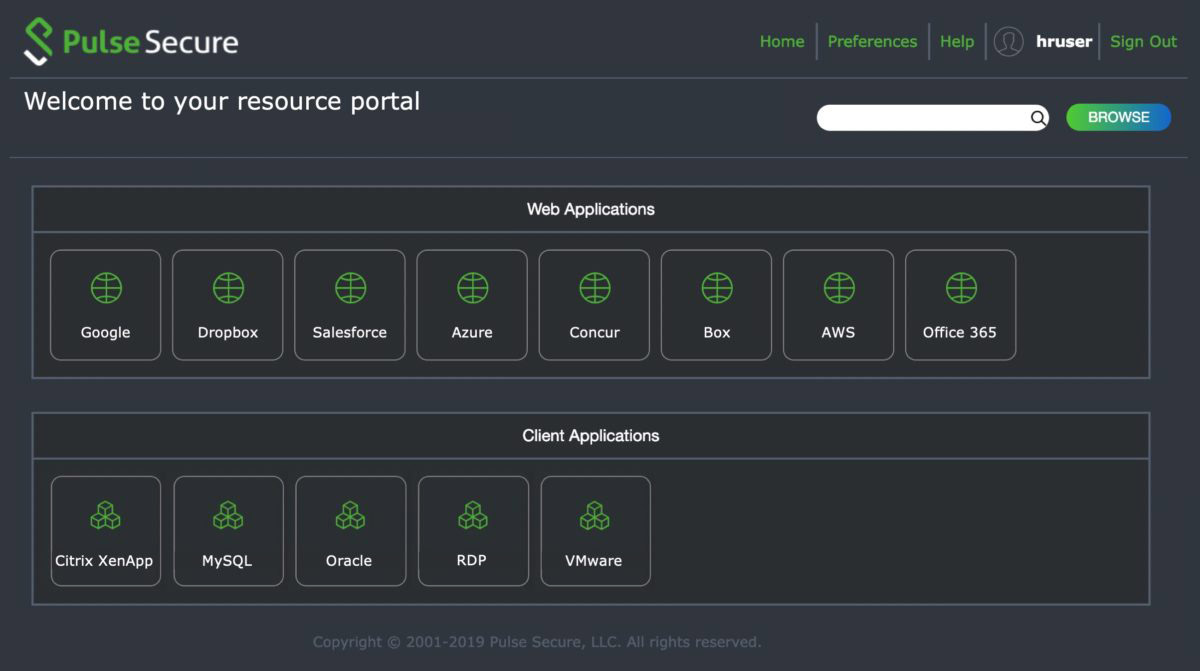
Pulse Secure and Travelex
Pulse Secure reported that a cybercriminal group had accessed their servers in April 2019.
The criminal group targeted Travelex, a forex and travel insurance company using Sodinokibi ransomware, also known as REvil.
The group contacted BBC demanding Travelex to pay $6million.
They had gained access to Travelex’s servers for six months and extracted five gigabytes of consumer data.
The cybercriminal group gave Travelex two days to pay the ransom with the promise of not using the private information and to restore its website.
It also threatened to sell the entire website if payment was not made in 7 days.
Security analysts discovered that Travelex had seven unpatched Pulse Secure.
This vulnerability was available on the internet bulletin boards from August 2019.
Hackers hit unpatched Fortinet SSL VPNs
Fortinet was attacked in May 2019 through a firmware update, which included security fixes.
After the Pulse Secure attack in April, Fortinet installed updated software, and yet this did not protect it.
At least 480,000 Fortinet Fortigate SSL VPN endpoints connected to the internet remained unpatched, and this is where attackers used to gain access.
Pulse Secure hacked by a Russian hacker
In August 2020, Pulse Secure found itself in trouble again when the login details and IP addresses of over 900 Pulse Secure VPN were posted on the dark web by a Russian-speaking hacker.
The information was posted in plain text, and anyone on the dark web can take advantage of it to blackmail Pulse Secure.
Researchers at Bank Security discovered the leak after they observed that the VPN servers posted by the hacker in the dark web were operating the firmware version containing CVE-2019-11510 vulnerability patched by Pulse Secure in early 2019.
The Department of Homeland Security has warned organizations to patch this critical vulnerability, which is one of the main weaknesses targeted by attackers.
Hackers use the stolen identities to crack enterprise networks even when Pulse Secure VPN vulnerability was patched.
7 Free VPNs leaked data for over 20 million users
While free VPNs do not guarantee the same security as enterprise VPNs, organizations and individuals still use free VPNs when browsing.
Security researchers at vpnmentor reported a massive data leak involving seven free VPN apps, namely UFO VPN, FAST VPN, Free VPN, Super VPN, Flash VPN, Secure VPN, and Rabbit VPN.
The VPNs stored over 1.2 terabytes of customer data, including 1,083,997,361 data records, including email addresses, clear text passwords, IP addresses, home addresses, and other personal information.
The seven VPNs claimed that they are “no-log” VPNs and do not store user data, and security researchers have found millions of user files.
VPNs Leaking Customer Data: Summing up
VPNs are vulnerable to attacks. You must invest in a reputable VPN that has the right safety measures to protect you on the internet.
Your VPN provider should use up-to-date encryption methods and change routing points regularly to maintain secure service.
Explore more information about VPN services to know what is the option to stay safe on the web.