The Definitive Guide To OT Security And Vulnerability Management
In this day and age, cyber threats are growing at an alarming rate. As a result, it is of utmost importance for organizations to take adequate measures to protect their operations and assets. One area of focus that often gets overlooked is OT (Operational Technology) security and vulnerability management.
This guide seeks to provide readers with the necessary insight into OT security and vulnerability management so they can better understand the risks associated with such networks and how to mitigate those risks. Read on to learn more about OT security and vulnerability management, from basic concepts to best practices.
What is OT Security management?
OT security management is the process of securing industrial control systems and networks. This includes identifying and mitigating these systems’ risks, vulnerabilities, and threats.
Every industry needs OT security management to protect critical infrastructure and industrial facilities from cyber attacks. OT cybersecurity is a proactive approach to protect you from cyberattacks that could cause physical damage to equipment or disrupt entire operations. Organizations must understand the potential risks and vulnerabilities to secure OT systems effectively. They also need to have robust security controls in place.
Some Common OT Security Risks
- Unauthorized access
Cybercriminals can gain access to OT systems through network breaches or social engineering. Once they have access, they can launch attacks that disable equipment or disrupt operations.
- Malicious code
Malware specifically designed to target OT systems can infect these systems and allow attackers to take control of them. This could lead to a loss of data or equipment damage.
- Denial of service
Attackers can launch denial of service (DoS) attacks against OT systems. This can cause equipment failures or disruptions in operations.
The Need for OT Security And Vulnerability Management
As the number of attacks on industrial control systems (ICS) and operational technology (OT) increases, it is clear that these systems are not adequately protected. Traditional security measures such as firewalls and anti-virus software are not designed to deal with specific threats to ICS/OT systems. There are several reasons why ICS/OT systems are particularly vulnerable to attack.
- Firstly, they often rely on outdated technology, which can be easily exploited.
- Secondly, they are often not well-protected from external networks, making them an easy target for attackers.
- Finally, ICS/OT systems often contain critical infrastructure information, which makes them a valuable target for hackers.
The need for OT security and vulnerability management is, therefore, clear. However, there are some challenges to implementing such measures.
- ICS/OT systems are often complex and challenging to secure.
- Many organizations do not have the necessary OT security framework to secure their ICS/OT systems effectively.
- The cost of securing ICS/OT systems can be prohibitive to some organizations.
Despite these challenges, organizations must take steps to secure their ICS/OT systems. There are a number of tools and OT security best practices to follow to improve OT security and vulnerability management. They include conducting risk assessments, implementing security controls, monitoring OT networks, and maintaining up-to-date documentation.
The Benefits of OT Security And Vulnerability Management
Operational technology (OT) security and vulnerability management are critical for ensuring the safety and resilience of industrial control systems (ICS). OT security encompasses the policies, procedures, and technical controls used to protect industrial equipment and systems from unauthorized access, use, disclosure, interception, or destruction.
Vulnerability management is a key component of OT security and refers to the process of identifying, assessing, and mitigating vulnerabilities in industrial systems. By proactively managing vulnerabilities, organizations can reduce the risks posed by potential threats to their operations.
There are many benefits to implementing an OT security framework and vulnerability management program:
- Reduced risk of cyber incidents: By identifying and addressing vulnerabilities in OT systems, organizations can reduce their exposure to cyberattacks.
- Improved safety: Addressing vulnerabilities can help improve safety by preventing or mitigating the effects of incidents on equipment or operations.
- Increased resilience: Managing vulnerabilities can help increase resilience by reducing the impact of incidents on operations. In some cases, it may even be possible to continue operations despite an incident.
- Improved compliance: Implementing an OT security policy and training can help organizations meet various compliance requirements related to critical infrastructure protection.
Overall, OT security and vulnerability management provide numerous benefits that can help organizations safeguard their industrial operations.
How to Secure Your OT Environment?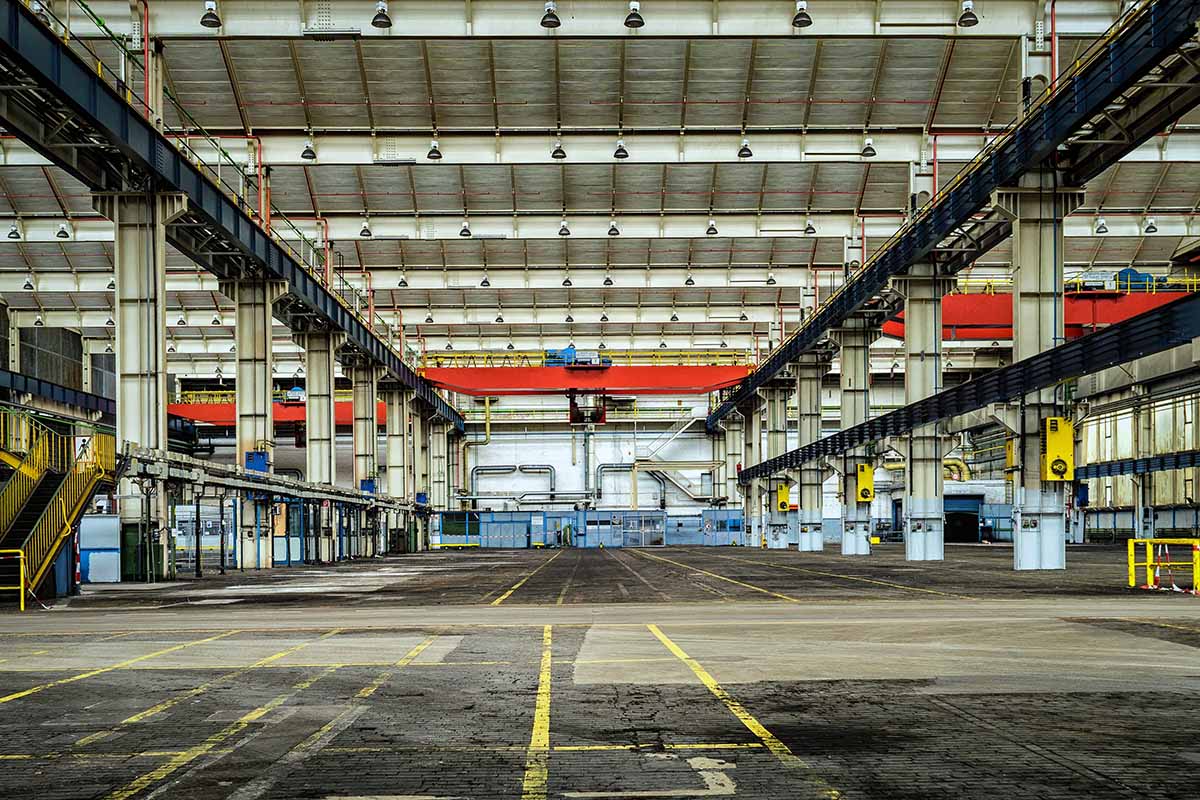
In the wake of industrial control system (ICS) and operational technology (OT) attacks like Stuxnet, Industroyer, and NotPetya, it’s clear that traditional IT security practices are not enough to protect critical ICSs. Organizations must take a holistic approach to OT security, including vulnerability management, access control, incident response, and network segmentation.
- Vulnerability management is a key part of OT security. Identifying and addressing vulnerabilities can help prevent attackers from exploiting them to access critical networks.
Regular OT security risk assessments can help identify potential vulnerabilities so they can be patched or mitigated.
- Access control is another important element. Limiting access to OT systems and networks to authorized users can help prevent unauthorized individuals from gaining access and making changes that could jeopardize the operation of critical systems.
Implementing role-based access control can help ensure that only authorized users have the necessary permissions to perform specific tasks.
- OT Incident response plan is essential for quickly identifying and responding to attacks on industrial systems. Having a well-defined incident response plan can help minimize the damage caused by an attack and get critical systems back up and running as quickly as possible.
- Network segmentation is another important element of an OT security strategy. Segmenting OT networks from IT networks can help isolate critical systems and limit the spread of an attack if one does occur.
Implementing firewalls and other perimeter defenses can protect segmented OT networks from external threats.
Conclusion
In conclusion, OT security and vulnerability management are essential parts of ensuring any organization’s safety and security. Organizations can ensure that their industrial systems are secure, reliable, and resilient by taking the time to understand the risks associated with OT systems, implementing the appropriate security measures, and providing employees with OT security training.
It is also important to employ OT security vendors or dedicated teams to regularly assess the security of these systems and update them as needed. By following the steps outlined in this guide, organizations can ensure that their OT systems are secure and properly managed.




















